What is Data Matrix Protection Suite?
Data Matrix Protection/Security Suite (DMPS) is an easy-to-use software package designed to Authenticate and/or encrypt Data Matrix symbol intended for use in Product Serialization, “Track and Trace”, Product Lifecycle Management or another common barcode applications, thus providing product/document protection from counterfeiting. With Data Matrix Security Suite, protecting your products and documents has never been quicker or easier!
DMPS consists of the two software programs – encoding (DMPS_E) and decoding (DMPS_D). Encoding software has a proprietary built-in mechanism allowing to enable authentication features in the encoded Data Matrix symbol or to encrypt it. The Decoding software checks symbol for authenticity or decrypts it while extracting the information from the symbol.
Depending on application, the programs can be used either together or separately. In a “Track and Trace”, for example, the encoding software can be used on the “manufacturing end” and the decoding software – on the “receiving end”.
Why do we need data label protection?
According to the International Chamber of Commerce (ICC) the global economic and social impacts of counterfeiting and piracy is estimated at US$1.7 trillion in 2015 and put 2.5 million legitimate jobs at risk each year. The figure is due in part to rapid increases in physical counterfeiting and piracy as measured by reported customs seizures and greater worldwide access to high speed Internet and mobile technologies. The international trade in fakes accounts for more than half of counterfeiting and piracy, and estimated to as much as US$960 billion.
Accordingly, counterfeiting data labels, designed to carry certain information about the product, has become one of the important steps in manufacturing fake products.
The rise of such fake products in different industries has driven strong requirements for anti-counterfeiting technologies to protect product integrity and company’s brands. This requirement calls for the new product - protective data label which can be either tracked from a factory to an end-user, or checked for legitimacy right at the POS.
How is DMPS symbol different from a regular Data Matrix?
DMPS technology extend the capability of Data Matrix from being just an “information tag” to authentication and/or encryption of this information. Protected Data Matrix does not look very much different from the regular one. “Authentication enabled” symbol actually looks identical and it can be decoded by any regular scanner. However, only 2DTG’s decoder can tell if this symbol is authentic or not:
| NO Protection | Authentication enabled | Encryption | Authentication + Encryption |
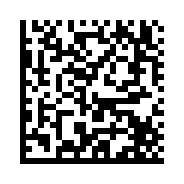 |
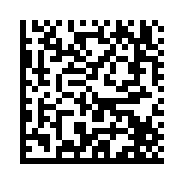 |
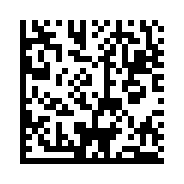 |
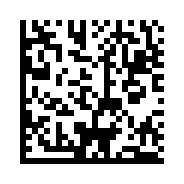 |
How does it work?
DMPS employs the concept of Digital Signature for data authentication. A digital signature scheme allows one “to sign an electronic message” and later the produced signature can be validated by the owner of the message or by any verifier. It normally utilizes asymmetric algorithm - a private key for signature generation, but a public key (which corresponds to, but is not the same as, the private key) - for signature verification. This is nearly always very computationally intensive and cannot be used on DSP-based platform (scanner).
Our patented method makes use of symmetric key algorithms integrated into the encoding/decoding mechanism. This makes our software suitable for embedded processing.
To strengthen the Authentication mechanism, DMPS also offers one more layer of protection - additional encryption (on top of authentication). This algorithm also satisfies the embedded processing requirements.
For the sake of convenience DMPS treats two above mentioned algorithms as two types of digital signatures – User Signature (Authentication) and Product Signature (Encryption). The term “signature” is used only to underline the fact that each Data Matrix, generated using these algorithms, will have the unique digital characteristics distinct from any other Data Matrix symbol with the same encoded message/data.
This uniqueness of the digital characteristics is “additionally reinforced” by including Data Matrix parameters into the Authentication/Encryption keys, as follows:
| Authentication Key | Encryption Key |
|
|
In other words, both Authentication and Encryption keys are calculated using all the data shown above as the input parameters. The length of this data string (input parameters) might be from 368 up to 2048 bits. Since the Authentication Key depends on encoded data sequence, it differs for every Matrix “going” through the Algorithm, which, in turn, makes it very difficult to break.
How difficult to integrate this technology with existing systems like Product Serialization, “Track and Trace”, etc.?
DMPS technology is a “natural extension” for those systems – from “tracking” to “tracking and protection”. It’s just simple software upgrade, which has Low (or “Zero”) impact on Product Price:
- NO set-up fee for authentication/encryption build-up
- NO special readers required for authentication
- NO impact on manufacturing process
- NO additional equipment necessary to apply the authentication during the manufacturing process - the printing of DMPS symbols easily assimilates within existing workflows
How this method can be used “in the field” (checking incoming products at loading deck, POS, etc.)?
2DTG offers mobile versions of DMPS_D software interfaced to Android, as well as DMPS Plugin for such widely used scanners/area images as Honeywell Xenon 1950/1952, Vuquest3320g, Granit 1910i/1911i, Voyager 1400g/1450g/1452g/1602g and N5600 scan engine. Some of these imagers might have already been used at those places. In such cases you do not even need new hardware to start reading protected Data Matrix symbols – you just upgrade your software to make it capable to perform authentication/encryption. These mobile versions include Keyboard Wedge APPs interfaced to DMPS Decoder – essentially, Authentication enabled data collection tool - and DMPS Reader to check product authenticity randomly.
Does 2DTG provide libraries for building customized APPs?
Yes, 2DTG provides DMPS SDKs both for Encoding and Decoding software interfaced to Windows XP…10/32 & 64 - sample project and decoding libraries. Decoding SDKs for Android 4.x and higher also available.
Can DMPS Decoder “read” DPM/Dot Peen symbols.
Yes, DMPS decoder also has DPM/Dot Peen capabilities extending its use to industrial applications.
Can Protection Suite software be used for protecting document exchange? Does it protect from direct coping?
Data Matrix Protection Suite (DMPS) by itself does not provide 100% protection from direct copying, but it makes the task of counterfeiting and copying symbols very difficult, or expensive, or both. It was designed first of all for “content protection” in supply chain (track & trace) applications or any other application that utilizes barcode as “information tag”. In such applications “barcode reproduction methods” are normally used as less expensive and more convenient for intruders in comparison with “direct copying”.
However, combination of DMPS technology with UV (Ultra-Violet) inks printing provides all three required components for documents/products protection (including ultimate protection from direct copying):
Authentication and/or Encryption and/or Validation
2DTG offers UV (Ultra-Violet) and IR (Infrared) scanners as an integral part of Barcode Protection strategy, supplementing content security - Barcode Security Suite – with safeguarding the label from direct copying.
Several major companies are now printing bar coded batch and lot control information on their products with this invisible ink to provide an indicator that the product is a legitimate one. If the data contained in the barcode mark are further authenticated using 2DTG’s protection technology, you can be assured that the item is legitimate, as well as not black market distribution, when the data is sent back to the manufacturer from the distribution channel.

